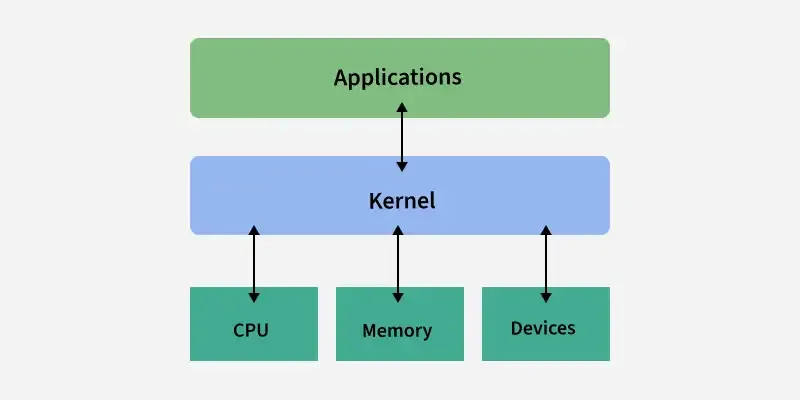
System Programming can be defined as the act of building Systems Software using System Programming Languages. According to Computer Hierarchy, Hardware comes first then is Operating System, System Programs, and finally Application Programs.
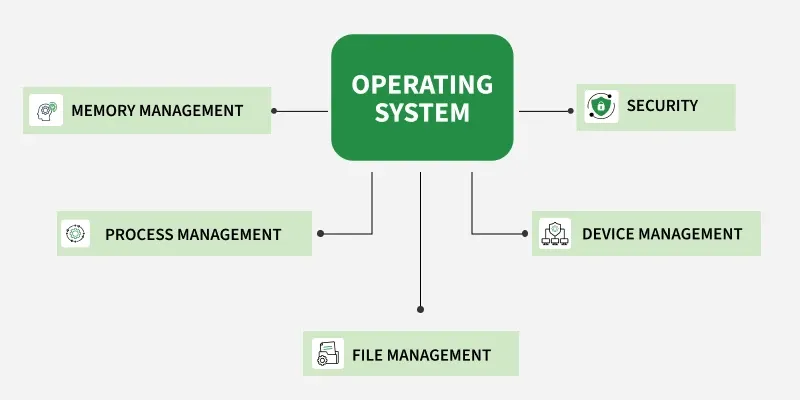
In the context of an operating system, system programs are nothing but a special software which give us facility to manage and control the computer's hardware and resources.
As we have mentioned earlier these programs work more closely with the operating system so it executes the operation fast and helpful in performing essential operation which can't be handled by application software.
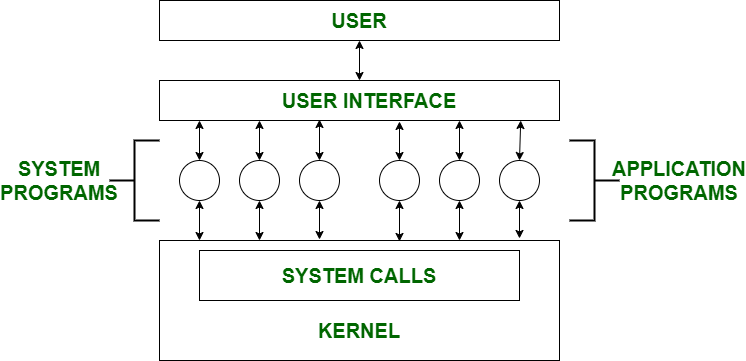
Note : The user can only view up-to-the System Programs he cannot see System Calls.
System Program Definition
System programs in an operating system are software tools that help users manage files, run programs, and control system resources. They include file managers, program loaders, compilers, and system utilities, making it easier to operate the computer efficiently and keep it running smoothly.
Here are the examples of System Programs :
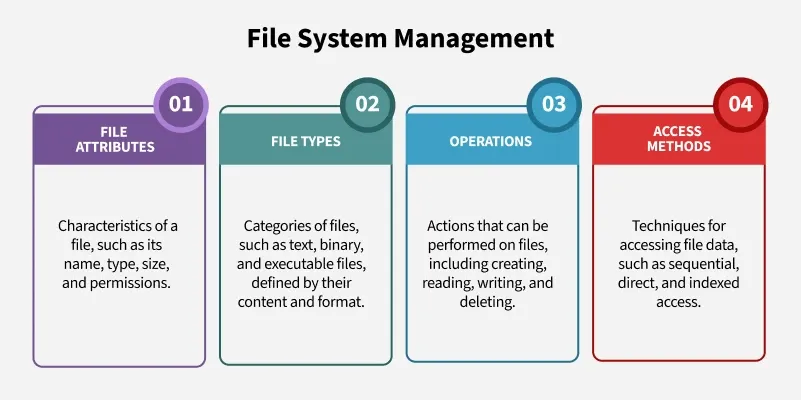
- File Management : A file is a collection of specific information stored in the memory of a computer system. File management is defined as the process of manipulating files in the computer system, its management includes the process of creating, modifying and deleting files.
- Command Line Interface(CLI's) : CLIs is the essential tool for user . It provide user facility to write commands directly to the system for performing any operation . It is a text-based way to interact with operating system. CLIs can perform many tasks like file manipulation, system configuration and etc.
- Device drivers : Device drivers work as a simple translator for OS and devices . Basically it act as an intermediatory between the OS and devices and provide facility to both OS and devices to understand each other's language so that they can work together efficiently without interrupt.
- Status Information : Information like date, time amount of available memory, or disk space is asked by some users. Others providing detailed performance, logging, and debugging information which is more complex. All this information is formatted and displayed on output devices or printed. Terminal or other output devices or files or a window of GUI is used for showing the output of programs.
- File Modification : This is used for modifying the content of files. Files stored on disks or other storage devices, we use different types of editors. For searching contents of files or perform transformations of files we use special commands.
- Programming-Language support : For common programming languages, we use Compilers, Assemblers, Debuggers, and interpreters which are already provided to users. It provides all support to users. We can run any programming language. All important languages are provided.
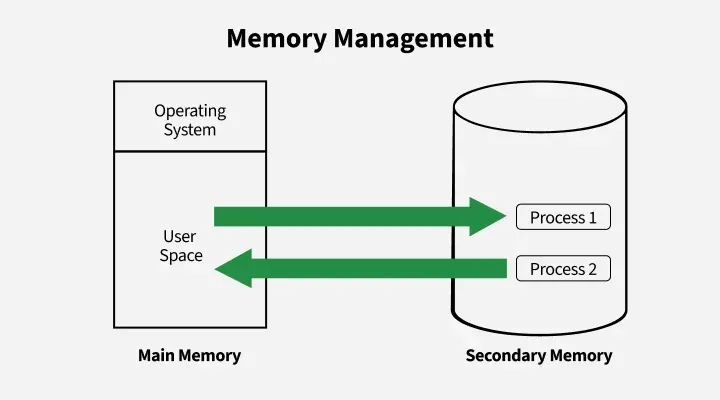
- Program Loading and Execution : When the program is ready after Assembling and compilation, it must be loaded into memory for execution. A loader is part of an operating system that is responsible for loading programs and libraries. It is one of the essential stages for starting a program. Loaders, relocatable loaders, linkage editors, and Overlay loaders are provided by the system.
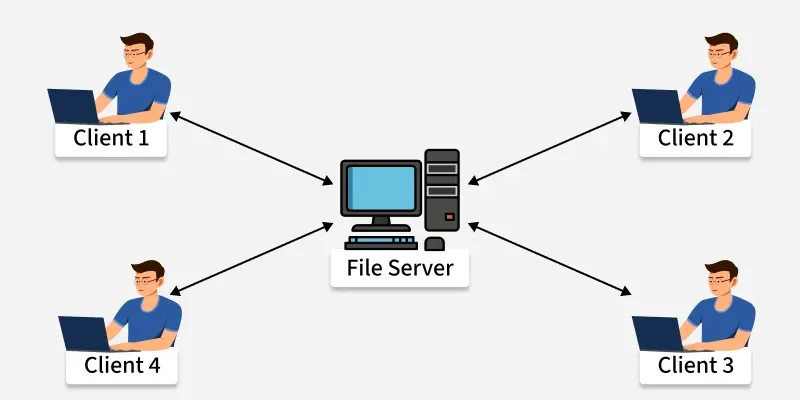
- Communications : Connections among processes, users, and computer systems are provided by programs. Users can send messages to another user on their screen, User can send e-mail, browsing on web pages, remote login, the transformation of files from one user to another.
Types of System Programs
Different types of system programs are:
- Device Drivers: Works as intermediaries between the operating system and hardware components. Without drivers, the OS cannot communicate effectively with devices like printers, keyboards, or graphic cards.
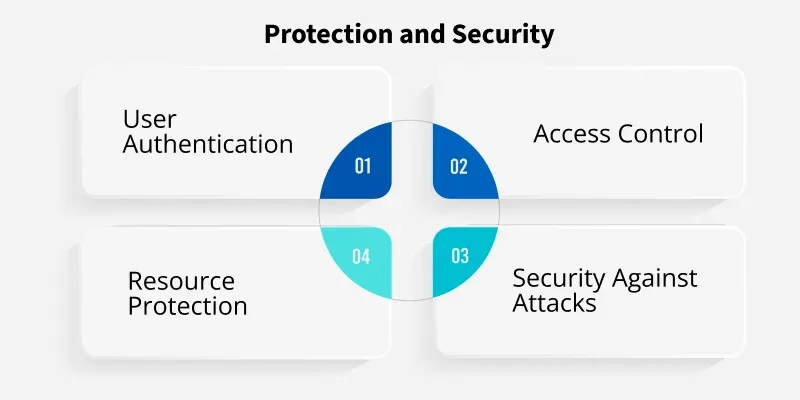
- Utility Program: Perform essential maintenance tasks to ensure the smooth functioning of the system. They include tools for disk cleanup, defragmentation, and antivirus protection, helping maintain system performance and security.
- Communication Programs: Enable data exchange between devices or users. User can send e-mail, browsing on web pages, remote login, the transformation of files from one user to another.
- File Management Programs: These programs create, delete, copy, rename, print, dump, list, and generally manipulate files and directories.
- Program loading and execution: Manage the process of loading executable programs into memory so they can run. The system may provide absolute loaders, relocatable loaders, linkage editors, and overlay loaders.
 Topic Wise Chapter in English
Topic Wise Chapter in English